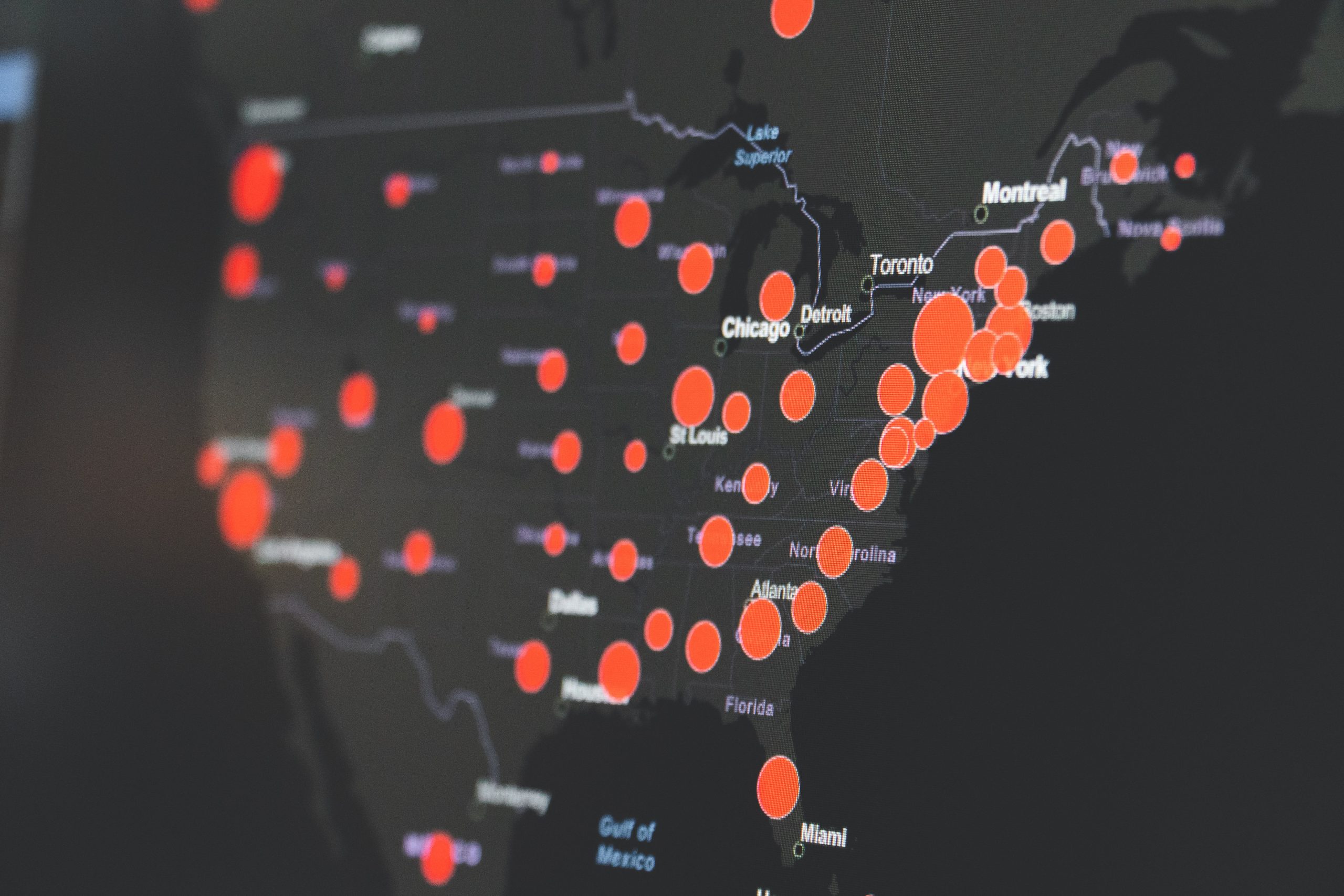
What Happened? Microsoft has reported four critical zero-day vulnerabilities for Microsoft Exchange Server that are actively being exploited by a state-sponsored threat group, HAFNIUM, and quickly expanding to other cyberattackers looking to take advantage of the vulnerabilities.
But seriously, folks.
Is this more of a theoretical threat? No, the vulnerabilities can be used in an attack chain leading to Remote Code Execution (RCE) which enables an attacker to hijack a server and install malware that can do any number of bad things: establish a back door, exfiltrate data, spread malware and execute system commands remotely. Cyberattackers are actively exploiting this vulnerability and the number of victims is rapidly growing.
Am I affected? This does not impact Exchange Online, rather it affects on-premise or hosted Exchange servers. Microsoft says Exchange 2010, 2013, 2016 and 2019 are affected, and therefore should be patched immediately.
Patching alone does not guarantee you are out of the woods.
Is this a simple fix? Not really. This is not a point and click resolution. While the patches can be downloaded from Microsoft and applied fairly easily, additional work is needed to check if you have already been compromised, in which case the patches will not protect you. Microsoft has provided an nmap script on GitHub to scan your network for vulnerable Exchange deployments, which requires the use of PowerShell. Microsoft has also created a script to run a check for HAFNIUM Indicators of Compromise (IOCs)
This is not a point and click resolution. You need to be comfortable with PowerShell and security concepts.
Where to go for help? Additional resources are available below. CREO is also available to assist our clients with patching and remediation processes. Contact me through LinkedIn or email me for assistance, rsummerville@creoinc.net.
Link to patch (please note the prerequisites): Released: March 2021 Exchange Server Security Updates – Microsoft Tech Community
IOC’s to look for: https://raw.githubusercontent.com/Azure/Azure-Sentinel/master/Sample Data/Feeds/MSTICIoCs-ExchangeServerVulnerabilitiesDisclosedMarch2021.csv
Script for validating the server is or is not compromised (Test-ProxyLogon): CSS-Exchange/Security at main · microsoft/CSS-Exchange · GitHub
CSS-Exchange/Test-ProxyLogon.ps1 at main · microsoft/CSS-Exchange · GitHub (direct link)
Information on IOC’s: HAFNIUM targeting Exchange Servers with 0-day exploits – Microsoft Security